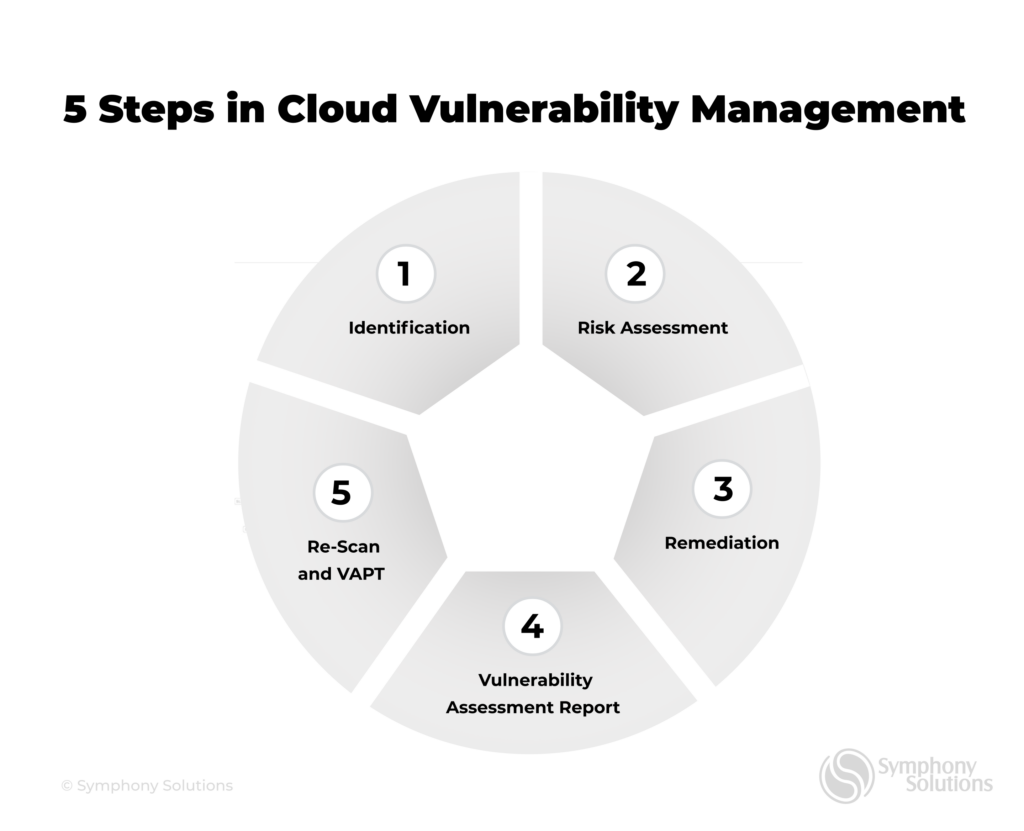
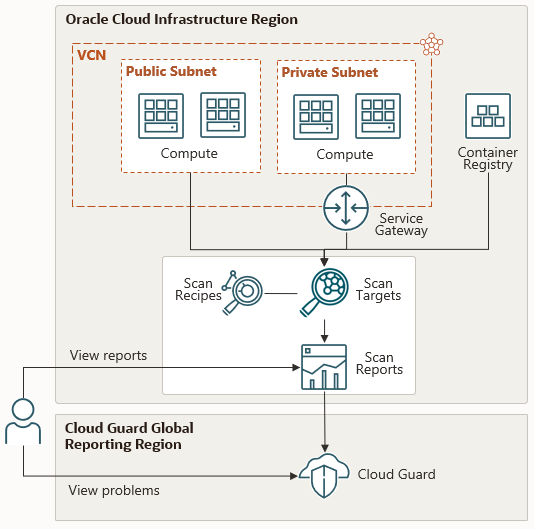
A guide to implement effective cloud vulnerability scanning | nasscom | The Official Community of Indian IT Industry
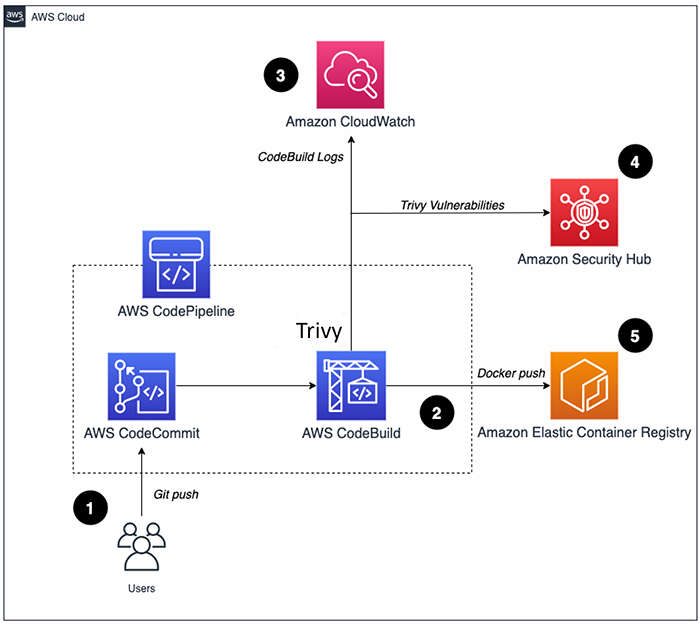
How to build a CI/CD pipeline for container vulnerability scanning with Trivy and AWS Security Hub | AWS Security Blog
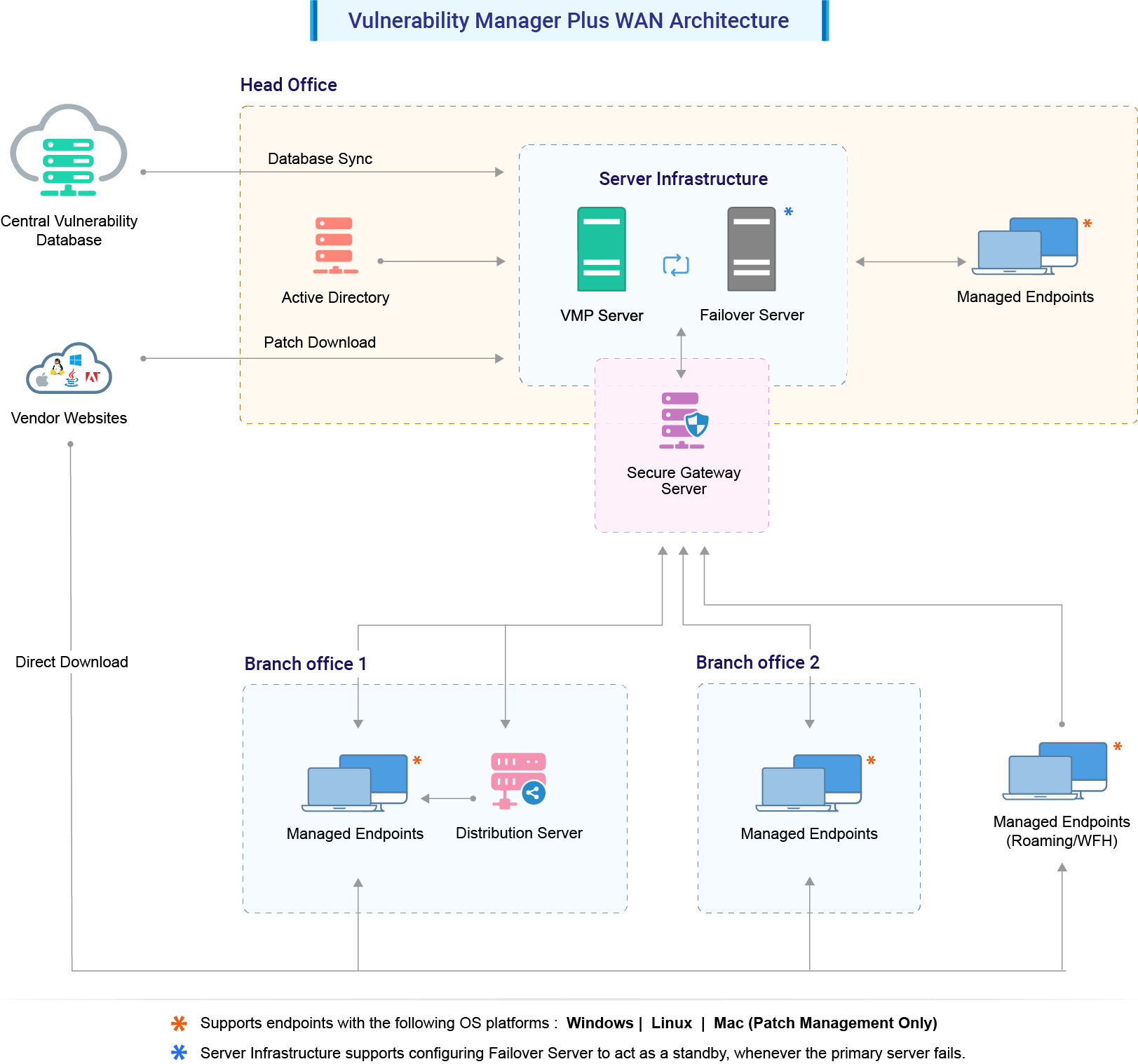
Vulnerability Scanner | Powerful Vulnerability Scanning Tools - ManageEngine Vulnerability Manager Plus






.png)